The website uses cookies to deliver services in accordance with the Cookies Policy. You can define the conditions for storing or accessing the cookie mechanism in your browser.
 11.10.2023
11.10.2023Data lifecycle management (DLM) is the process of appropriately securing data throughout its lifespan. Its basic stages are creation, storage, use, sharing and destruction.
Figure 1. 6 basic stages of data lifecycle management
The goal of DLM is to ensure data security and regulatory compliance at all stages without compromising business productivity. This requires the application of different processes and principles at different phases of the cycle.
It's important to remember that data lifecycle management is closely related to information lifecycle management (ILM), but there is a subtle difference between them. DLM deals with raw data such as files and databases and their attributes: file type, size and age. ILM, on the other hand, goes a step further and takes into account the information in a file or database record and how different pieces of data are combined. A lot of raw information is stored in various silos and may include messages such as a company purchase order. Both DLM and ILM can include both structured and on-premises or cloud-based content.
Three main goals of data lifecycle management
The most important goals of data lifecycle management are the three elements of the CIA triad:
- Confidentiality – data must be protected against unauthorized access, disclosure or theft,
- Integrity – data must be authentic, accurate and reliable. One integrity risk is having multiple versions of the same data and no clear indication of which version is reliable; to prevent such spread of data, it is necessary to manage it effectively,
- Accessibility – Because business relies on data, it is critical that data is accessible to authorized users through search or other navigation methods. Accessibility also includes the efficient processing and visualization of data to support business strategy.
Phases of data lifecycle management
The six basic parts of the DLM presented earlier can be presented in a more descriptive way.
- Creation – data may be prepared internally or collected by IT systems. For example: users both receive and send emails, and their browsers often store cookies and search history,
- Storage - once created, data is kept in databases and data warehouses, file shares, etc. It must be classified according to its sensitivity and value, including what regulations it is subject to to guide its management and protection processes such as access control, encryption and loss prevention data (DLP),
- Use – data will be used by various stakeholders: from business users to customers and partners. Often, their analysis and visualization is based on enterprise resource planning, human resources, consumer relationship management and related applications,
- Sharing – Users often need to share data with others. DLMs must ensure that it is limited only to what is necessary and permitted under internal rules and external regulations,
- Archiving – data that is no longer used is most often stored on tape, disk or in the cloud. Archiving is valuable for data that cannot be destroyed due to business needs or regulatory requirements. They can be archived in the original format or in the form of, for example, a screenshot or export. They are often encrypted,
- Destruction – Data that is no longer used or stored can be deleted. However, it is worth asking whether they can be reused.
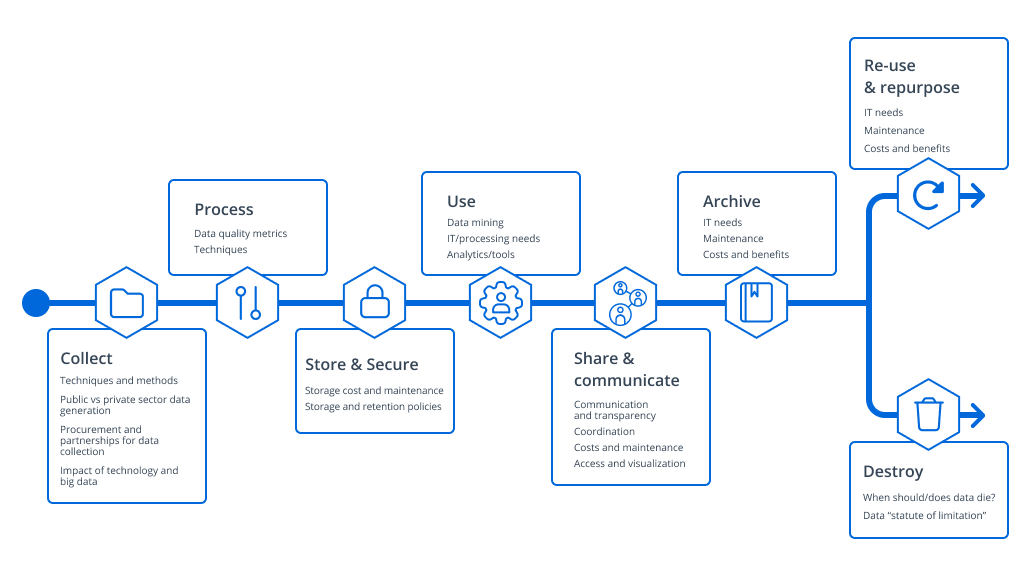
Figure 2. Detailed breakdown of data cycle management phases
How Netrwix can help?
Modern organizations often store petabytes of data, both structured and unstructured, in multiple silos, so effective DLM is not possible using manual methods. Netwrix allows you to manage the entire data cycle from one pane.
If you want to learn more about the solution, please contact Damian Malinowski, who is the solution manager at Bakotech.
Contact Us
Bakotech Sp. z o.o.
Dane firmy
VAT ID 6762466740
REGON 122894922
KRS 0000467615
Kontakt
ph. +48 12 340 90 30