The website uses cookies to deliver services in accordance with the Cookies Policy. You can define the conditions for storing or accessing the cookie mechanism in your browser.

Flowmon Packet Investigator
Automated PCAP analyzer
Flowmon Packet Investigator (FPI) is a network traffic auditing tool that automatically records and analyzes full packet data. Combining automated PCAP analysis and built-in expert knowledge, it provides you with an instant deep understanding of emergent issues and offers suggestions for a remedy.
SOLUTION OVERVIEW
Instant analysis
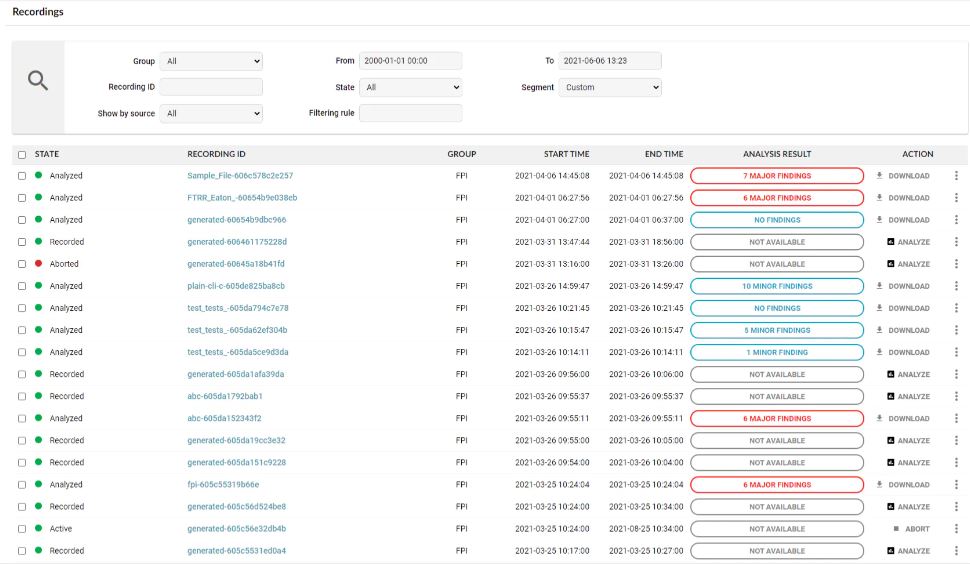
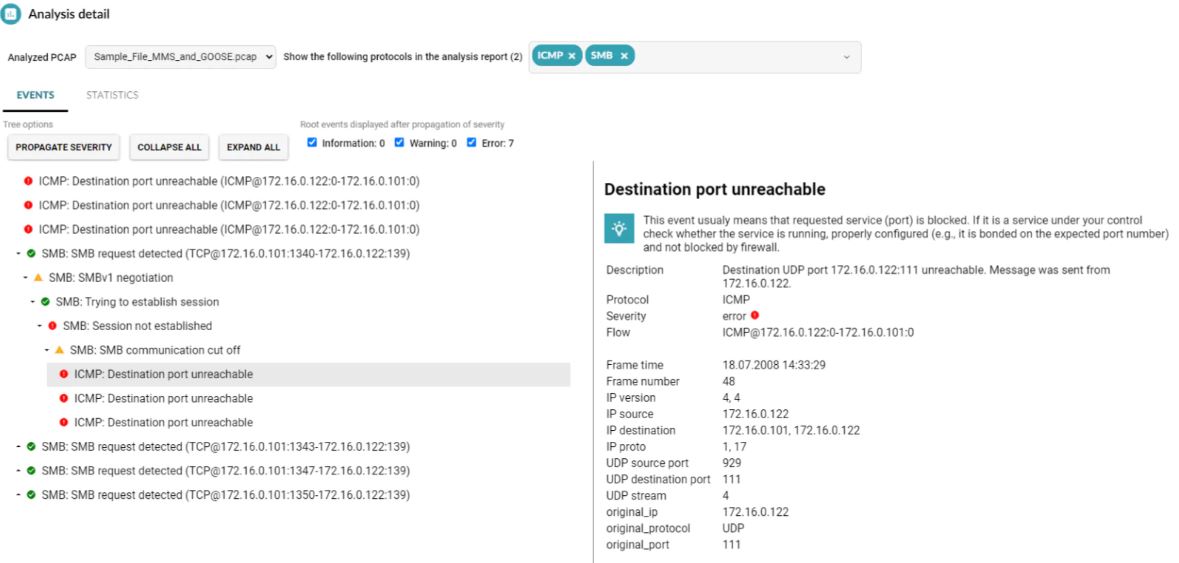
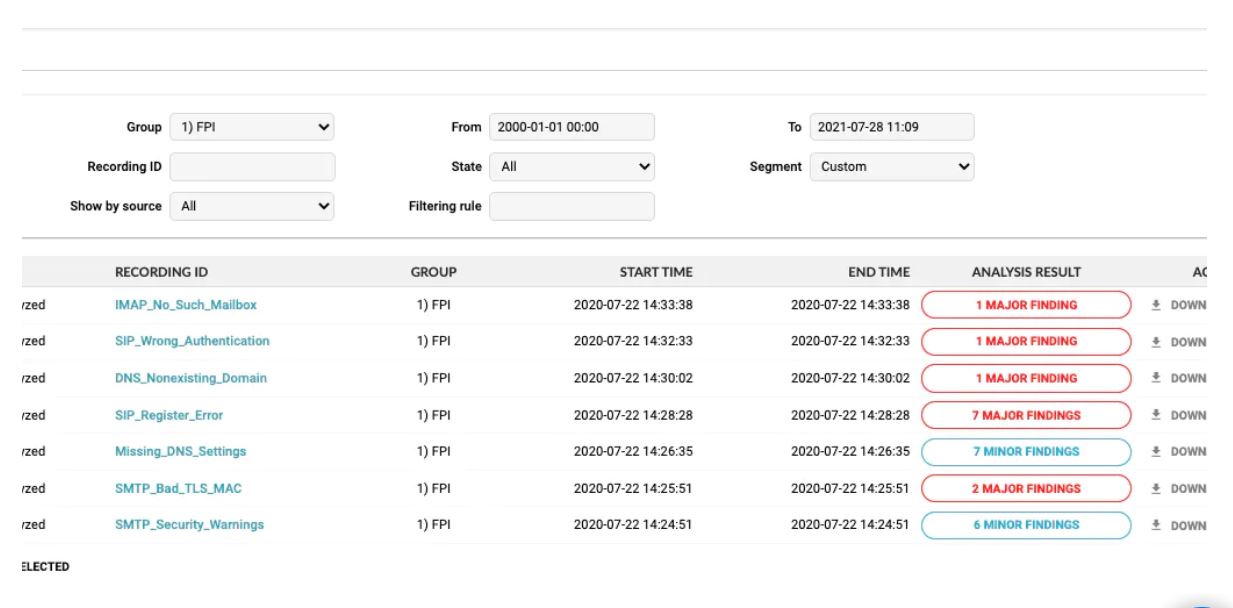
The Flowmon Packet Investigator performs an automatic decision-tree analysis of network protocols, their dependencies, RFC specifications and errors from a PCAP file, giving you an immediate number of issues found as well as their severity.
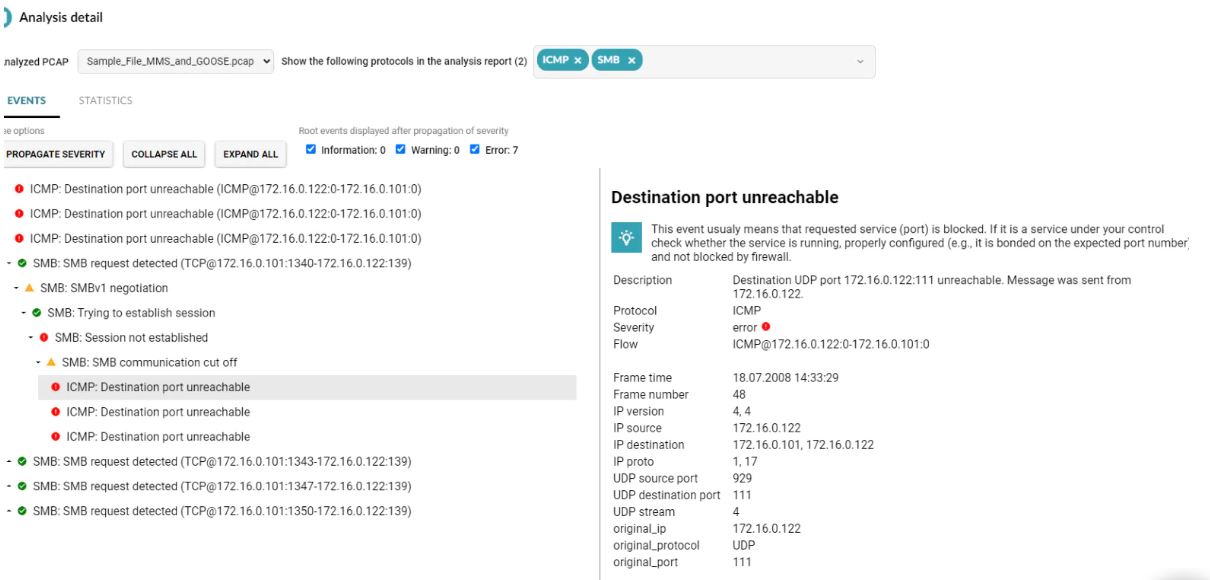
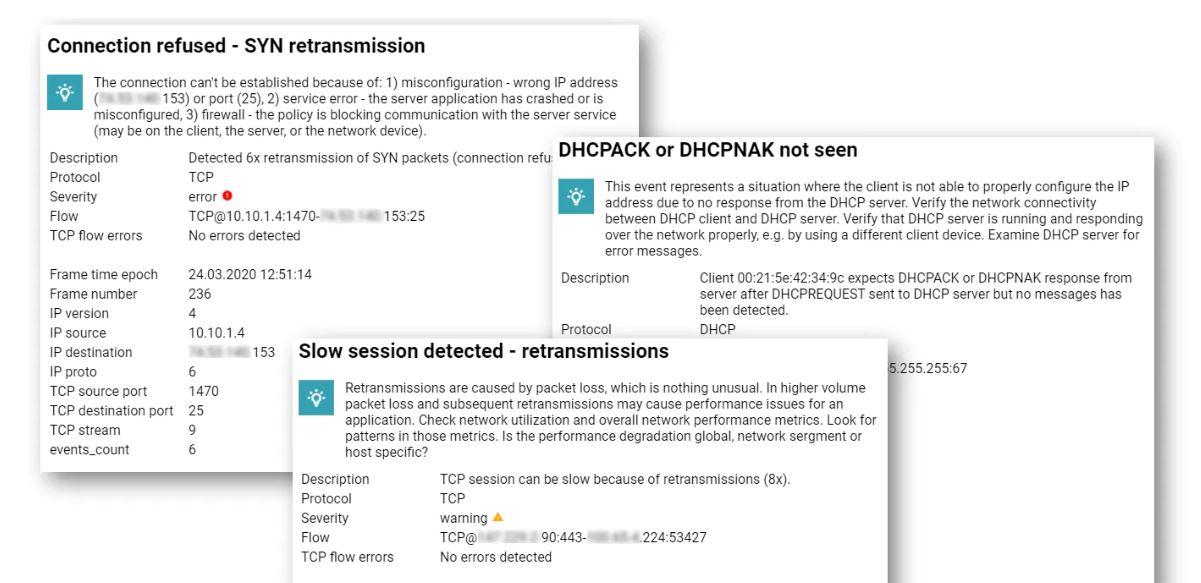
Built-in expertise
The FPI houses decades of combined networking experience provided by our in-house experts. By expanding the analysis results, you can browse through the individual analysis steps and see explanations of the possible root-cause of issues including recommendations for remedial action.
Automatic capture
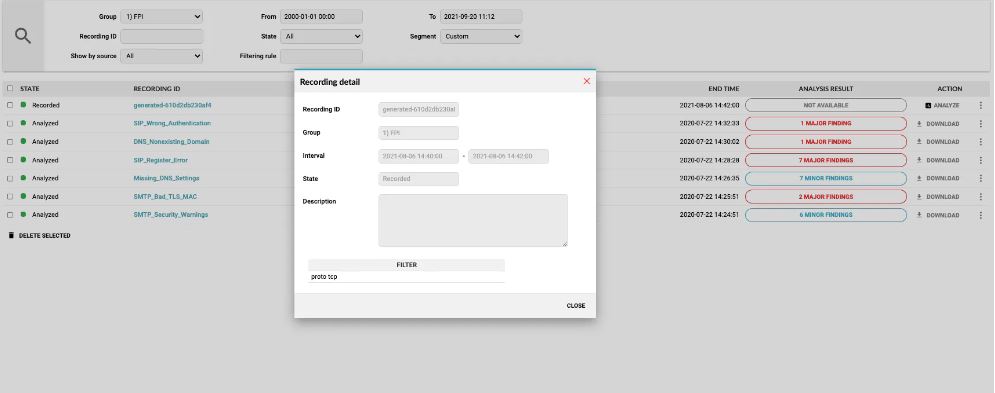
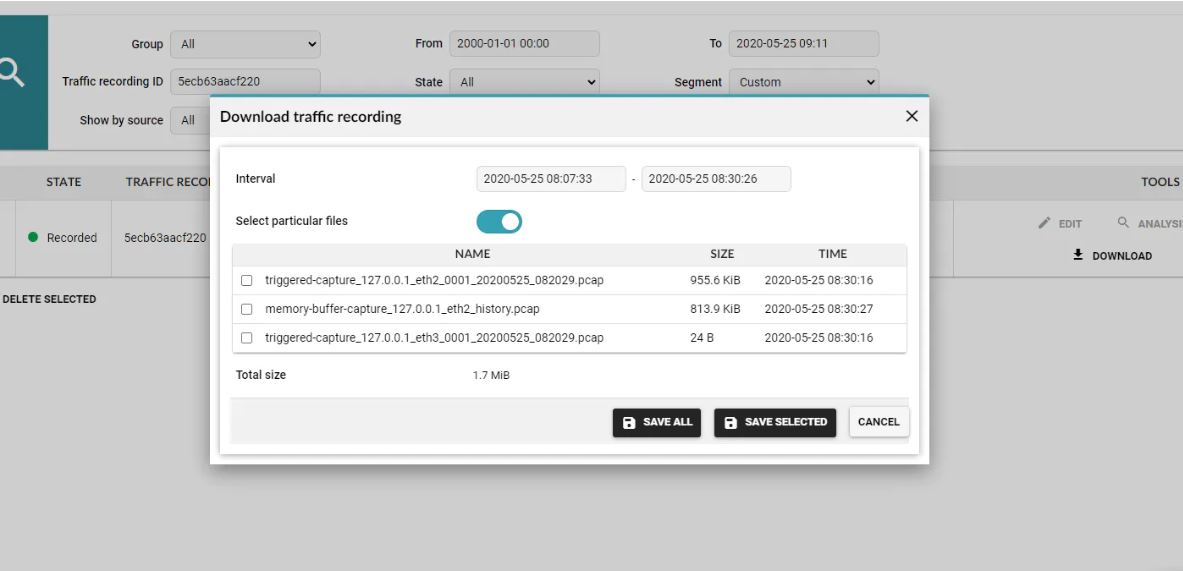
Never drop a packet. You can record packets manually, upload your own PCAP files or the FPI can performed automated policy-based packet capture, e.g. upon security event detection, at speeds of 1G–100G. The rolling buffer retains a number of packets from before the event occurred, making sure that no history is lost.
Functional versatility
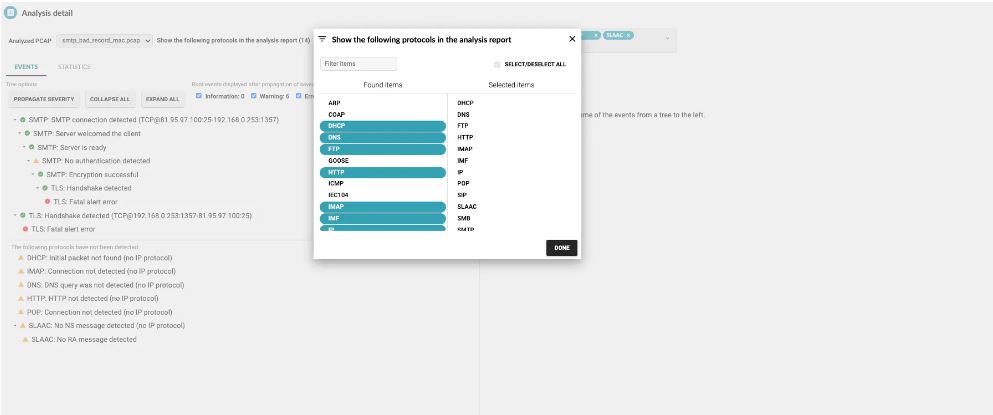
The FPI is built to cover a broad spectrum of protocols with the number constantly rising. Identify malfunctions or misconfigurations of critical network devices (ARP, DNS, DHCP, ICMP, NTP), expose client/server encryption incompatibility (SSL/TLS version, encryption algorithms, certificates), application protocol stack issues (HTTP, Samba, FTP, IMAP, POP, etc.) or IoT issues (CoAP, IEC104, GOOSE, MMS, MQTT).
STAGES OF AUTOMATED PACKET ANALYSIS
1. Getting the data
The FPI captures full-packet traces on-demand via automated, manual, and scheduled triggers, or lets you upload your own file.
2. Analyzing the PCAP
The analytical engine investigates the packet traces via an intelligent decision-tree analysis.
3. Looking for errors
The FPI looks for RFC deviations and unexpected occurrences and translates the errors into intelligible explanations.
4. Visualizing the results
You can see the number and severity of issues located with the option to view the full analysis right away.
FEATURES:
Locate the root cause
Autonomous investigation of DHCP, DNS, FTP, IMAP, IMF, POP, SIP, SLAAC, SMB, SMTP, IP, TCP, SSL, HTTP.
Reduce MTTR
Let the analytical engine locate the root-cause, describe it and recommend a solution.
Record your traffic
On-demand and on-event L2-L7 network traffic recording (packet sniffing).
IT solutions

Test a product
On local martkets Bakotech Group operates through a well-established partner network, including over 1,000 active dealers. Key IT-integrators and are involved in the realization of large-scale projects concerning implementing solutions for end-customers from various segments of business. Bakotech's business strategy is True Value Added Distribution or in other words - project oriented distribution.
We are providing our partners with a wide range of services such as PR, co-marketing activities, pre post-sales support, trainings for partners and end-customers, PoC, PoV, solution consulting, implementation support and technical support.
Contact Us
Bakotech Sp. z o.o.
Dane firmy
VAT ID 6762466740
REGON 122894922
KRS 0000467615
Kontakt
ph. +48 12 340 90 30